🚨 Introduction
In 2026, the biggest risk to your ISP business isn't competition.
It's a security breach you never saw coming.
Every day, ISPs across the world face:
- 🔴 DDoS attacks that knock entire networks offline
- 🔴 RADIUS credential theft and unauthorized access
- 🔴 Rogue subscribers bypassing billing controls
- 🔴 Unmonitored routers acting as entry points for attackers
- 🔴 Zero-day vulnerabilities in unpatched network hardware
Without a proper security and monitoring framework, your ISP is one attack away from financial loss, reputation damage, and regulatory consequences.
This guide covers everything you need to know about securing your ISP network in 2026 — from common threats to real-world monitoring strategies using Zal Ultra ISP CRM.
🎯 Why ISP Security Is Different (And Harder)
Unlike a regular business network, an ISP infrastructure is uniquely exposed:
1. You are the internet for your customers Every attack that hits your network affects your subscribers too. Downtime means lost revenue — and lost trust.
2. Your network is always on ISPs operate 24/7. There's no "closing time." Attackers know this and exploit off-hours when your team is asleep.
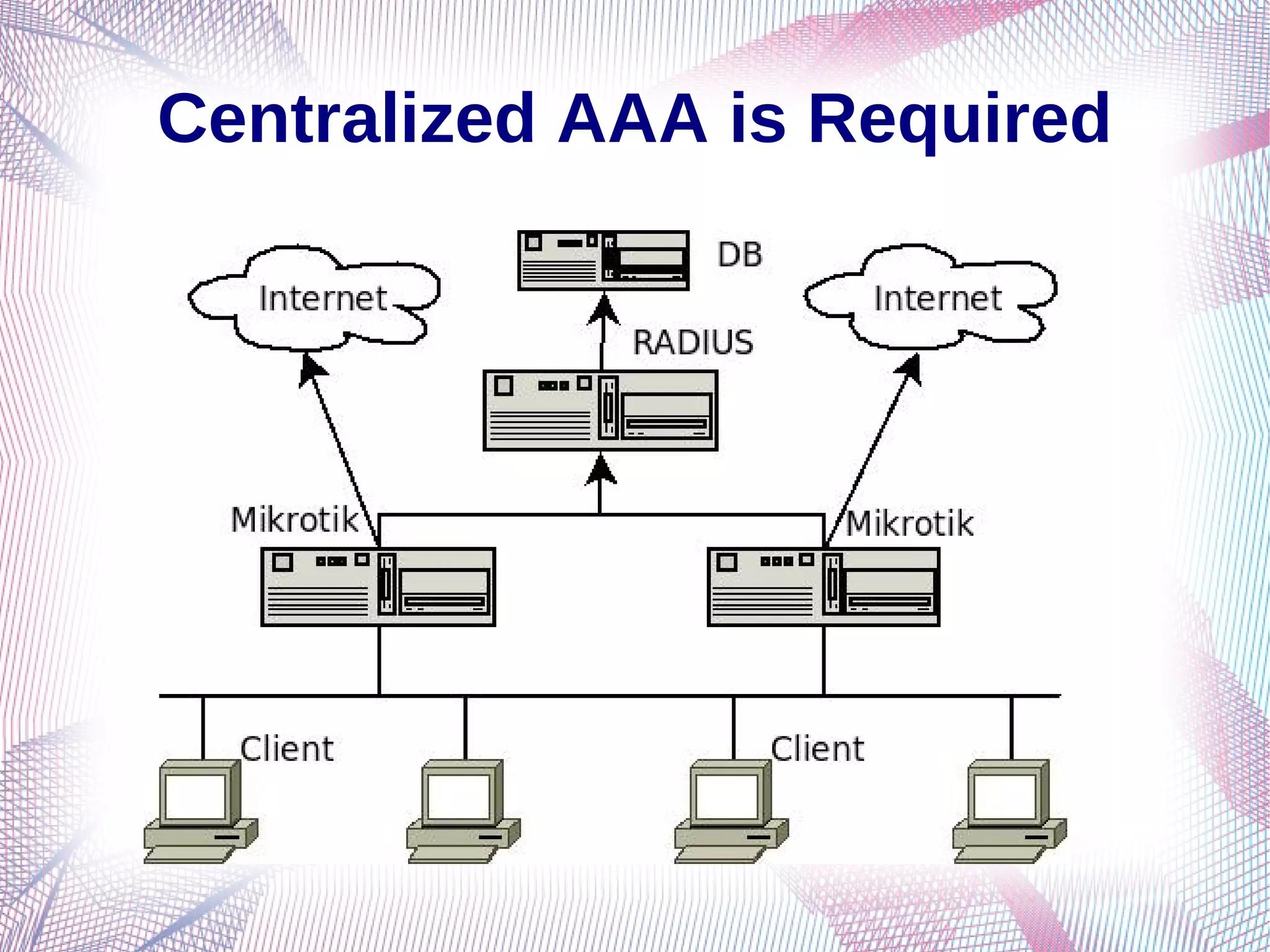
3. You manage hundreds (or thousands) of devices Routers, switches, NAS devices, RADIUS servers — each one is a potential vulnerability if not properly monitored.
4. RADIUS is your crown jewel — and a prime target Your RADIUS server controls authentication for every single subscriber. If it's compromised, your entire network is exposed.
👉 This is why ISP security isn't optional. It's survival.
🔥 Top 5 Security Threats Facing ISPs in 2026
⚡ Threat #1: DDoS Attacks
Distributed Denial of Service (DDoS) attacks flood your network with traffic — overwhelming routers, servers, and bandwidth pipes.
Real-world impact:
- Network goes offline for hours or even days
- Customers migrate to competitors
- Revenue loss per hour can be catastrophic
How to defend:
- Deploy upstream DDoS mitigation via your transit provider or CDN
- Use rate-limiting rules on MikroTik/edge routers
- Monitor traffic spikes in real time using Zal Ultra's live network dashboard
🔐 Threat #2: RADIUS Authentication Bypass
If attackers crack your RADIUS credentials, they can:
- Authenticate as legitimate users
- Steal bandwidth without paying
- Access and leak subscriber data
How to defend:
- Use strong, rotating shared secrets on all RADIUS NAS entries
- Whitelist NAS IP addresses in FreeRADIUS
- Enable RADIUS accounting logs and review them regularly
- Use Zal Ultra ISP CRM to automatically flag unusual login patterns
🕵️ Threat #3: Rogue Subscribers & Bandwidth Theft
Some customers attempt to:
- Clone MAC addresses to hijack another subscriber's session
- Share PPPoE credentials across multiple devices
- Exploit IP allocation misconfigurations for free access
How to defend:
- Enable MAC binding in all subscriber profiles
- Restrict simultaneous logins per account using the RADIUS
Simultaneous-Useattribute - Use IP/MAC mismatch alerts built into your CRM system
🛠️ Threat #4: Unpatched & Misconfigured Routers
Every unpatched router on your network is a door left open.
Common vulnerabilities:
- Default Winbox/SSH credentials never changed
- Outdated RouterOS firmware with known public exploits
- Management interfaces exposed directly to the public internet
How to defend:
- Maintain a firmware update schedule for all MikroTik/Cisco/Ubiquiti devices
- Disable Telnet and all unneeded management services
- Restrict management access to a dedicated admin VLAN only
- Audit all router config changes through Zal Ultra's activity logs
📡 Threat #5: Syslog & Log Blindness
Most ISPs generate thousands of log events per hour — and ignore 99% of them.
Without centralized log monitoring, you will never detect:
- Failed authentication attempts (brute force attacks)
- Config changes made by unauthorized or rogue staff
- Hardware failures silently degrading performance before they cause downtime
How to defend:
- Deploy a centralized syslog solution like ABC Syslog Server by Onezeroart
- Set up real-time alerts for critical events
- Review weekly security reports generated by your CRM
🛡️ The ISP Security Framework: 4 Core Pillars
A secure ISP in 2026 is built on 4 pillars:
🔒 Pillar 1 — Authentication Security
Goal: Ensure only legitimate users can access your network.
✅ Use RADIUS with strong shared secrets ✅ Enforce password complexity for all subscriber accounts ✅ Enable CoA (Change of Authorization) for instant session control ✅ Automatically disable or lock inactive accounts
👉 Zal Ultra ISP CRM automates subscriber authentication via its built-in FreeRADIUS 3.x integration — giving you full, real-time control over every session.
📊 Pillar 2 — Real-Time Network Monitoring
Goal: Know exactly what is happening on your network, right now.
✅ Monitor bandwidth usage per subscriber ✅ Track active sessions and detect anomalies instantly ✅ Receive alerts on abnormal traffic patterns (potential DDoS early warning) ✅ View device uptime and connectivity status from a central dashboard
👉 Zal Ultra's admin dashboard provides live visibility across your entire ISP infrastructure — no separate third-party monitoring tools needed.
📋 Pillar 3 — Centralized Log Management
Goal: Capture, store, and analyze every important network event.
✅ Collect syslog data from all routers and servers in one place ✅ Instantly search logs when troubleshooting incidents ✅ Generate compliance reports for auditors or business investors ✅ Detect brute-force attacks from repeated failed login attempts
👉 ABC Syslog Server by Onezeroart is purpose-built for ISPs. It centralizes logs from MikroTik, Cisco, Ubiquiti, and other vendors — giving your team the visibility they need, 24/7.
🚀 Pillar 4 — Incident Response Readiness
Goal: When something goes wrong, respond fast and contain the damage.
✅ Assign clear roles: Who handles a DDoS? Who contacts an affected subscriber? ✅ Create runbooks for common incidents: router down, RADIUS failure, subscriber compromise ✅ Test your incident response plan at least once every quarter ✅ Use Zal Ultra's staff management to maintain a full audit trail of who did what and when
⚙️ Practical Security Setup: Step-by-Step
✅ Step 1: Audit Your Current Security Posture
Before you can fix vulnerabilities, you need to find them.
Run through this checklist right now:
- Are all router default passwords changed?
- Are management interfaces restricted by IP or VLAN?
- Is RADIUS using strong shared secrets on every NAS?
- Are subscriber sessions being logged and monitored?
- Do you have a syslog server collecting events from all routers?
- Are billing suspensions and network access synchronized automatically?
If you answered No to any of these — that's where you start.
✅ Step 2: Harden Your RADIUS Server
Using Zal Ultra's built-in FreeRADIUS, configure the following:
- NAS IP whitelist — Only allow known, registered routers to query RADIUS
- Strong shared secrets — Minimum 32-character random strings, rotated every 90 days
- Simultaneous-Use = 1 — Prevent credential sharing between multiple devices
- Accounting interval — Set to 60–300 seconds for accurate, real-time session tracking
- CoA auto-disconnect — Cut sessions instantly the moment a subscriber is suspended
✅ Step 3: Set Up a Router Security Baseline
For every MikroTik (or other vendor) router on your network:
- Change all default admin credentials immediately
- Enable SSH access, disable Telnet entirely
- Restrict Winbox access to your admin VLAN only
- Enable syslog forwarding to your centralized log server
- Apply strict firewall rules to limit who can reach management interfaces
✅ Step 4: Deploy Centralized Syslog Monitoring
Point all your routers to ABC Syslog Server and configure:
- Syslog destination IP on every device
- Severity levels: Warning, Error, and Critical
- Alert rules for:
- 3+ failed login attempts within 5 minutes → immediate alert
- Any configuration change → log and notify
- Any interface going down → real-time notification
✅ Step 5: Enable Subscriber Anomaly Alerts in Zal Ultra
- Set bandwidth threshold alerts per subscriber package
- Enable MAC address mismatch notifications
- Configure auto-suspension triggers for expired or overdue accounts
- Review the active session report every week — look for anything unusual
📈 Real ISP Scenario: Stopping a Breach Before It Happens
The situation: A regional ISP with 800 subscribers noticed unusual traffic at 2:00 AM — a single subscriber account was suddenly generating 10× its normal upload traffic.
Without monitoring: The attack goes undetected until morning. By then, the congestion could knock hundreds of customers offline. The ISP loses revenue, trust, and subscriber goodwill — all overnight.
With Zal Ultra + ABC Syslog Server:
- Bandwidth anomaly alert triggers at 2:03 AM
- Admin receives an SMS and email notification immediately
- Session is force-disconnected via CoA in under 5 minutes
- ABC Syslog Server preserves the full event timeline for investigation
- Account is flagged for review. MAC address is blocked from re-connecting.
Result: Zero downtime for other customers. Breach contained. Evidence preserved. Subscriber notified.
👉 This is what professional ISP security looks like in 2026.
🔧 Onezeroart Security Stack: Tools at a Glance
| Tool | Role | Key Benefit |
|---|---|---|
| Zal Ultra ISP CRM | Core ISP platform | Built-in RADIUS, real-time sessions, auto-billing |
| ABC Syslog Server | Log management | Centralized syslog from all router vendors |
| MikroTik firewall rules | Edge security | DDoS rate-limiting, IP/MAC filtering |
| FreeRADIUS 3.x | Authentication engine | CoA, Simultaneous-Use, IP pool control |
💡 Frequently Asked Questions
Q: Do I need a separate security tool if I'm already using Zal Ultra? Not necessarily. Zal Ultra handles authentication security, session monitoring, and subscriber anomaly detection out of the box. For deep log analysis and router event correlation, ABC Syslog Server adds a powerful second layer.
Q: How do I prevent DDoS attacks from taking down my whole network? Work with your upstream transit provider to enable BGP blackhole routing for attack IPs. At the edge, configure MikroTik raw firewall rules to rate-limit and filter known attack traffic patterns.
Q: What is the single most common security mistake ISPs make? Using default or weak RADIUS shared secrets — and never reviewing authentication logs. These two issues alone are responsible for the majority of real-world ISP security incidents.
Q: Can Zal Ultra disconnect a subscriber immediately if I suspect a compromise? Yes. Using CoA (Change of Authorization), you can terminate any active session directly from the Zal Ultra dashboard in real time — no need to log into the router manually.
🏁 Conclusion: Security Is Not an Afterthought
In 2026, ISP security is a core business requirement — not a nice-to-have.
The ISPs that survive and scale are the ones that:
✅ Monitor their networks continuously — not just when something breaks ✅ Automate their responses to security events ✅ Use integrated, purpose-built tools like Zal Ultra ISP CRM and ABC Syslog Server ✅ Build documented processes and train their teams to follow them
Don't wait for a breach to take security seriously.
Start your free demo of Zal Ultra ISP CRM today — and see how easy professional-grade ISP security can actually be.